If cybersecurity frameworks sound like something only large enterprises worry about, you’re not alone. Most small and mid-sized businesses assume frameworks like NIST are too complex, too technical, or just not built for them.
That’s a mistake.
The reality is, the NIST Cybersecurity Framework was designed to be flexible. It’s not a rigid checklist. It’s more like a roadmap that helps businesses understand where they are, where they need to go, and how to get there without overcomplicating things.
For growing businesses handling customer data, financial information, or internal systems, having a structured approach to cybersecurity is no longer optional. It’s essential.
This guide breaks down NIST recommendations in a way that actually makes sense for small and mid-sized businesses. No jargon overload. No unnecessary complexity. Just practical steps you can start using.
What Is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework (CSF) is a set of guidelines that helps organizations manage and reduce cybersecurity risk.
Instead of telling you exactly what tools to use, it focuses on outcomes. What should your business be able to do to stay secure?
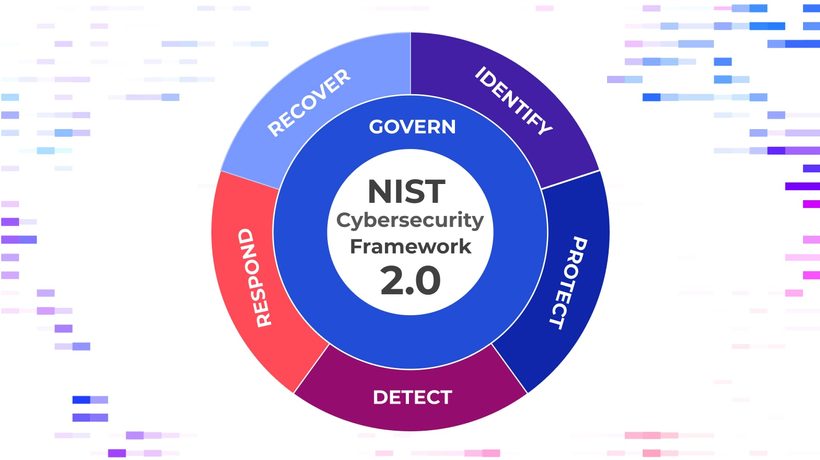
At its core, the framework is built around five key functions:
Identify, Protect, Detect, Respond, and Recover.
Think of these as stages in your cybersecurity journey rather than technical requirements. Each function helps you build a more complete and resilient security posture.
Why NIST Matters for Small and Mid-Sized Businesses 
A lot of SMBs assume frameworks are only for compliance-heavy industries or massive corporations. But here’s the thing: cybercriminals don’t think that way.
Smaller businesses are often easier targets because they typically lack structured security programs. That’s exactly where NIST becomes valuable.
It gives you a structured way to:
- Understand your risks
- Prioritize security investments
- Create repeatable processes
- Improve over time without starting from scratch
Even better, you can implement it gradually. You don’t need a full security team or massive budget to get started.
How NIST Compares to Other Cybersecurity Frameworks
Not every business starts with NIST. Some look at other frameworks like ISO 27001, CIS Controls, or even industry-specific standards.
So why does NIST stand out?
The biggest advantage is flexibility. Unlike more rigid frameworks, NIST doesn’t force you into a strict certification process. It allows businesses to adopt what makes sense based on their size, risk level, and available resources.
For small and mid-sized businesses, this is a big deal. You’re not locked into heavy documentation or expensive audits just to get started.
Another key difference is accessibility. NIST is written in a way that focuses on outcomes rather than technical instructions. That means you don’t need deep cybersecurity expertise to begin implementing it.
Compared to something like ISO 27001, which is more compliance-driven, NIST is more practical and operational. It helps you build a working security program rather than just checking boxes.
For most SMBs, NIST acts as a strong foundation. You can always layer additional frameworks later if needed.
 Breaking Down the 5 Core Functions of NIST
Breaking Down the 5 Core Functions of NIST
Identify: Know What You Have
Before you can protect anything, you need to know what exists in your environment.
This includes devices, software, data, and user access.
Most businesses skip this step and jump straight into buying tools. That usually leads to gaps and wasted spend.
Start by creating a simple inventory:
- What systems do you use?
- Where is sensitive data stored?
- Who has access to what?
This clarity alone reduces a surprising amount of risk.
Protect: Put Safeguards in Place
Once you know what you have, the next step is protection.
This includes basic but critical controls like:
- Strong access controls
- Multi-factor authentication
- Data encryption
- Employee training
This is where many SMBs already have tools in place, but they’re often not configured properly.
Protection isn’t about having more tools. It’s about using the right ones correctly.
Detect: Spot Problems Early
No system is 100% secure. The goal isn’t perfection, it’s awareness.
Detection focuses on identifying suspicious activity before it turns into a full-blown incident.
This can include:
- Monitoring login activity
- Tracking unusual behaviour
- Setting up alerts for anomalies
Early detection can be the difference between a minor issue and a major breach.
Respond: Act Quickly and Effectively 
When something goes wrong, speed matters.
A response plan ensures your team knows exactly what to do during an incident.
Without a plan, businesses waste critical time figuring things out in the moment.
A simple response plan should answer:
- Who is responsible?
- What steps should be taken?
- How will communication be handled?
Even a basic plan is far better than none.
Recover: Get Back to Normal
After an incident, the focus shifts to recovery.
This includes restoring systems, recovering data, and getting operations back on track.
Backups play a huge role here.
If your backups aren’t tested or easily accessible, recovery becomes much harder than it needs to be.
Recovery also includes learning from the incident so you can improve moving forward.
How to Start Implementing NIST Without Overwhelm
The biggest mistake businesses make is trying to implement everything at once.
That’s not how NIST is meant to be used.
Instead, start small.
Pick one area, usually Identify or Protect, and build from there.
For example:
- Create an asset inventory
- Enable multi-factor authentication
- Train employees on phishing awareness
These small steps create momentum.
Over time, you can expand into detection, response planning, and recovery strategies.
Quick Wins You Can Implement This Month
If the full framework still feels like a lot, the easiest way to start is by focusing on quick wins.
These are small changes that don’t require a huge budget or technical expertise but still make a meaningful impact.
Start with access control. Make sure every employee is only accessing what they actually need. Over-permissioned accounts are one of the most common security gaps.
Next, enable multi-factor authentication across all critical systems. This single step can prevent a large percentage of account compromise attacks.
Another easy win is employee awareness. A short training session on phishing emails can drastically reduce risk.
You should also review your backup strategy. Make sure backups are automated, stored securely, and tested regularly.
Finally, create a simple incident response checklist. It doesn’t need to be perfect. Just having a basic plan puts you ahead of most businesses.
These quick wins build confidence and create a strong starting point for deeper NIST alignment.
 Common Mistakes SMBs Make with NIST
Common Mistakes SMBs Make with NIST
Even with a flexible framework, there are a few common pitfalls.
One of the biggest is overcomplicating things.
Businesses often try to replicate enterprise-level implementations, which leads to frustration and stalled progress.
Another mistake is treating NIST as a one-time project.
Cybersecurity isn’t static. Your business changes, your risks change, and your security approach needs to evolve with it.
Some organizations also focus too heavily on tools instead of processes.
Tools are important, but without clear policies and workflows, they don’t deliver real value.
Aligning NIST with Everyday Business Operations
One of the best things about NIST is that it doesn’t require you to rebuild your business from scratch.
Instead, it fits into what you’re already doing.
For example:
- Your onboarding process can include access control policies
- Your IT setup can include security configurations
- Your employee training can include cybersecurity awareness
When security becomes part of everyday operations, it stops feeling like an extra task.
It just becomes how your business runs.
The Role of Leadership in NIST Implementation 
One thing that often gets overlooked in cybersecurity is leadership involvement.
Many businesses treat security as an IT responsibility, but NIST adoption works best when leadership is actively involved.
Why?
Because cybersecurity decisions often impact budget, priorities, and company culture.
If leadership doesn’t support security initiatives, they tend to stall or get deprioritized.
On the other hand, when leadership is engaged, things move faster. Policies are enforced more consistently, and employees take security more seriously.
Leadership doesn’t need to understand every technical detail. What matters is understanding the business risk.
When decision-makers recognize that cybersecurity is tied to revenue, reputation, and operations, it becomes a priority instead of an afterthought.
Measuring Progress Without Getting Technical
You don’t need advanced metrics to know if you’re improving.
Simple questions can give you a clear picture:
- Do we know what systems we have?
- Are critical accounts protected with MFA?
- Do we have a response plan?
- Are backups tested regularly?
If the answer to these questions improves over time, your security posture is improving.
NIST is about progress, not perfection.
How to Prioritize Security Investments Using NIST
One of the most practical benefits of NIST is how it helps you decide where to spend your time and money.
Instead of guessing or reacting to the latest threat, you can prioritize based on risk.
Start by identifying your most critical assets. This could be customer data, financial systems, or operational tools.
Then ask a simple question: what would happen if this was compromised?
The higher the impact, the higher the priority.
From there, map your current controls against NIST functions. Are you protecting those assets properly? Can you detect issues quickly? Do you have a response plan?
This approach helps you avoid overspending on low-impact areas while ignoring critical risks.
For SMBs with limited budgets, this kind of prioritization is essential.
 Making NIST Work Long-Term
Making NIST Work Long-Term
The real value of NIST comes from consistency.
It’s not about implementing everything perfectly. It’s about building habits and improving over time.
Set a regular schedule to review your security posture.
This could be quarterly or even twice a year.
Look at what’s working, what’s missing, and what needs improvement.
Small, consistent improvements are far more effective than one big effort followed by inaction.
What a “Good” NIST Implementation Actually Looks Like
A common misconception is that you need to fully implement every part of NIST to be considered secure.
That’s not true.
A “good” implementation is one that fits your business.
For some companies, that might mean having strong access controls, basic monitoring, and a tested backup system.
For others, it could include more advanced detection tools and formal response processes.
The goal isn’t perfection. It’s coverage.
You want to make sure that across the five core functions, there are no major gaps.
Even a simple, well-maintained setup is far more effective than a complex system that no one understands or uses properly.
Consistency beats complexity every time.
Future-Proofing Your Business with NIST 
Cyber threats aren’t slowing down. If anything, they’re becoming more sophisticated.
Having a structured framework like NIST puts you in a much stronger position to adapt.
It helps you make smarter decisions, prioritize effectively, and respond faster when something goes wrong.
For small and mid-sized businesses, that’s a huge advantage.
Instead of reacting to problems, you’re proactively managing risk.
If you’re not sure where your business currently stands or how to start implementing NIST the right way, the next step is getting clarity. A quick conversation with cybersecurity professionals can help you identify gaps, prioritize actions, and build a roadmap that actually works for your business.
FAQ
Is NIST only for large organizations?
No. The framework is designed to be flexible and can be scaled to fit businesses of any size.
Do I need a cybersecurity expert to implement NIST?
Not necessarily. Many basic steps can be implemented internally, though expert guidance can speed up the process.
How long does it take to implement NIST?
It depends on your starting point. Most SMBs can begin seeing improvements within weeks by focusing on key areas.
Is NIST required by law?
In most cases, no. However, it is widely recommended and sometimes required in regulated industries.
What’s the biggest benefit of using NIST?
It provides a clear, structured way to manage cybersecurity risk without unnecessary complexity.
Related Articles
- NIST Cybersecurity Framework 2.0: What Changed
- Building a Security Program That Aligns with NIST
- Mapping NIST Controls to Real-World SMB Environments