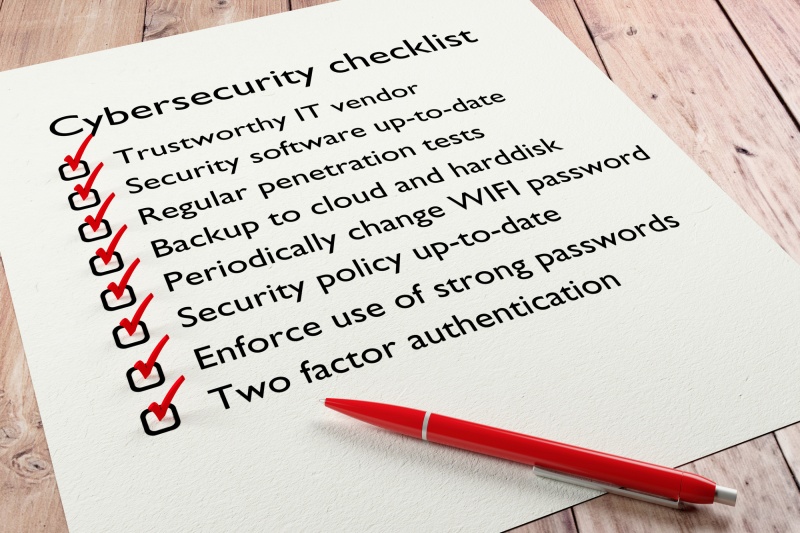
Cyber Hygiene: The Five Security Tasks You Should Complete Before Year-End
As the year winds down, most businesses are busy closing projects, finalizing budgets, and planning for the next quarter. But there’s one more thing you don’t want to forget before flipping the calendar: cyber hygiene. Just like routine health check-ups keep you healthy, good cyber hygiene keeps your digital environment resilient, protected, and ready for whatever the new year brings. Below are […]
Cyber Hygiene: The Five Security Tasks You Should Complete Before Year-End Read More »